Help
Forum
The community forum is a place to give and receive help with the NetFoundry platform’s web console, API, etc…
Customer Support
Learn more about contacting customer support in Support Hub.
Improve this Site
Contributions are welcome! This site is open-source. You may create a branch or a fork on GitHub and send a pull request. Learn how to edit this site.
Minor changes may be made directly in GitHub’s online editor wherever Edit appears at bottom-right.
Foundational Concepts
Organization
An organization is a consolidated billing and ownership domain comprising network Groups. Read articles about organizations
Network Group
A network group is a collection of networks. Read articles about network groups
Network
A NetFoundry network is a management domain and collection of resources e.g. endpoints, services, edge routers (and edge router policies), and AppWANs.
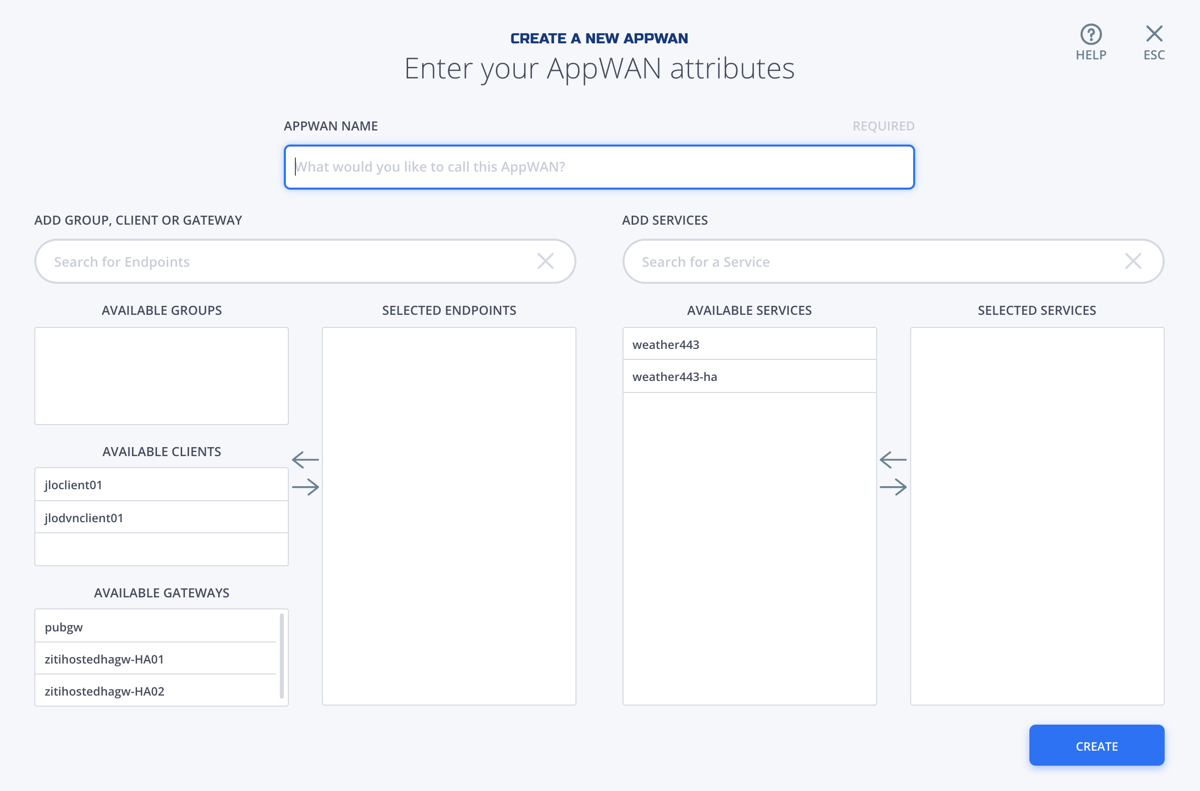
AppWAN
An AppWAN is a policy that controls access to services and it works like a permission group. In the web console, An AppWAN is visually represented as endpoints on the left that are allowed to connect to services on the right. Read articles about AppWANs.
Endpoint
An endpoint is node on the edge of your network. Protected traffic flows to, from, and through endpoints. endpoints may be configured to dial or host services, or both.
Service
A service describes a server and determines which AppWANs will grant access. A service is hosted by some device which must be able to reach the server. Read articles about services.
Edge Router
An edge router is an enrolled instance of ziti-router, typically auto-configured by NetFoundry by way of “registration”. Edge routers typically perform one of two primary functions: hosting a service in your branch or data center (customer-hosted edge routers), or listening for dialing endpoints in a NetFoundry data center (hosted edge routers). Edge routers automatically form the mesh overlay fabric by creating links to the hosted edge routers in NetFoundry data centers. Read articles about edge routers.
NetFoundry VM
The NetFoundry VM is a deployable system image with pre-installed software for a variety of virtual network functions e.g. customer-hosted edge router, gateway tunneler, Linux router. NetFoundry offers a variety of virtual machine system image formats that can be imported in your preferred VM stack or launched by on your preferred cloud.
The best way to obtain the latest VM for your network is to create an edge router and then visit its detail page in the console and click “get the VM” and follow the stack-specific instructions found there.
Tunneler
Tunnelers are a category of endpoint softwares and may be used to connect a device to the network. This approach is an alternative to connecting a site to the network with a gateway or connecting an app to the network with an SDK.